Overview
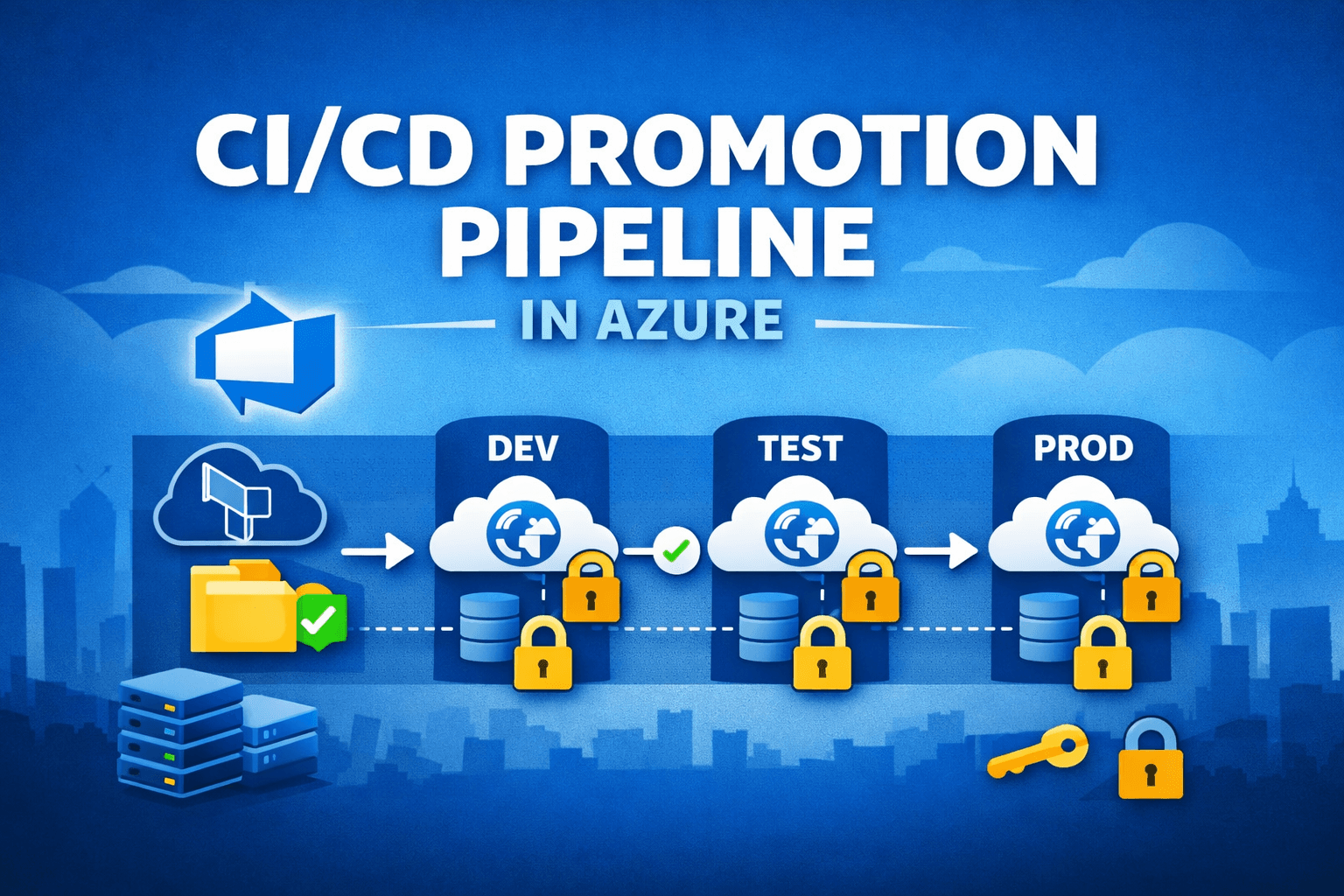
This reference implementation demonstrates a structured CI/CD promotion model for Azure-based applications.
The focus is not on application complexity, but on platform engineering fundamentals:
- Build once, promote across environments
- Infrastructure as Code with Terraform
- Secretless deployments using Managed Identity
- Clear environment separation (Dev → Test → Prod)
- Approval-based promotion model
The project simulates a typical enterprise scenario where CI/CD pipelines and infrastructure evolve organically and require consolidation into a stable, traceable structure.
Context
In many Azure environments, common patterns emerge over time:
- Hardcoded or pipeline-managed secrets
- Manual infrastructure changes
- Direct production deployments
- Rebuild-per-environment instead of artifact promotion
- Limited traceability across stages
This project explores a structured alternative aligned with enterprise delivery practices.
Architecture
Promotion Flow
Build → Dev → Test → Prod
- The application is built once.
- The artifact is promoted across environments.
- Terraform provisions infrastructure per environment.
- Test and production deployments require manual approval.
Each environment contains:
- Azure App Service (Linux)
- Azure Key Vault
- System-assigned Managed Identity
- Dedicated Terraform state
No infrastructure or secrets are shared across environments.
CI/CD Design
The pipeline is structured into independent stages:
- Build
- Terraform Plan / Apply (per environment)
- Application Deployment
- Approval Gates (Test / Prod)
Key principles:
- Artifact immutability
- Environment promotion instead of rebuild
- Infrastructure and application deployment separated
- Reusable pipeline templates
- Health checks after deployment
This structure ensures traceability, rollback capability, and controlled release flow.
Infrastructure as Code
Terraform is organized into:
infrastructure/├── modules/├── environments/│ ├── dev│ ├── test│ └── prod└── bootstrap/
Design considerations:
- Modular resource definitions
- Remote state with locking (Azure Storage backend)
- Explicit environment isolation
- Clear naming conventions
- Minimal privilege assignments
This approach supports predictable deployments and reduces configuration drift.
Security Model
Security design focuses on eliminating static credentials.
Implemented patterns:
- Managed Identity for application authentication
- Azure Key Vault for secret management
- RBAC-based access control
- No secrets in source code
- No secrets embedded in pipeline YAML
The application uses DefaultAzureCredential to support both local development and cloud execution without credential duplication.
Legacy Comparison
The repository includes a legacy branch illustrating common CI/CD anti-patterns such as:
- Hardcoded credentials
- Monolithic pipelines
- No environment separation
- Direct production deployments
- Manual infrastructure provisioning
This comparison highlights structural differences between ad-hoc setups and promotion-based delivery models.
Engineering Considerations
Key aspects explored during implementation:
- Terraform state locking and concurrency handling
- Dependency ordering for Managed Identity and RBAC
- Promotion gating strategy
- Artifact version traceability
- Environment configuration isolation
The objective was architectural clarity rather than feature richness.
Key Learnings
- Promotion-based CI/CD improves deployment traceability
- Infrastructure modularization reduces long-term maintenance cost
- Managed Identity simplifies credential management
- Clear environment separation supports operational stability
- Pipeline structure matters more than pipeline length
Scope
This is a focused reference implementation intended to demonstrate:
- Azure platform engineering fundamentals
- CI/CD architecture patterns
- Infrastructure automation practices
- Security-aware cloud design
It is intentionally limited in application scope to keep the emphasis on platform structure.
Status: Completed Reference Implementation
Last Updated: February 2026